Pyrit allows you to create databases of pre-computed WPA/WPA2-PSK PMKs. By using Multi-Core CPUs and ATI-Stream,Nvidia CUDA, and OpenCL, it is a powerful attack against one of the world's most used security-protocols. Wifi kali wifi kali linux 2020 kali linux 2020.4 wifite wifite2 wifite2 kali linux wpa wep wps alfa comptia cech oscp. Please note that links listed may be affiliate links and provide me with a small percentage/kickback should you use them to purchase any of the items listed or recommended. Thank you for supporting me and this channel!
rockyou wordlist is a password dictionary used to help to perform different types of password cracking attacks. It is the collection of the most used and potential passwords.
Many Password cracking tools are used dictionary attack method, in this case, you will have a requirement of password wordlist.
So Offensive Security has added already many dictionaries in Kali Linux by default, RockYou wordlist is one of the biggest dictionaries.
Rockyou wordlist in Kali Linux 2019.3
First, rockyou wordlist was added in the backtrack and later it was added in Kali Linux 1. This is the first version of kali Linux launched in 2013.
I have eyes on Kali Linux from the born of it. by the way, using Kali Linux awesome. You can create your own dictionary during a password cracking attack.
You can use crunch and cwel for creating a wonderful dictionary. But if you are a beginner and just want to test tools or practice the tool, then RockYou wordlist is good for you.
Location of Rockyou wordlist
Trust me or not, you can’t remember rockyou location if I will tell you. Right now I don’t know the location exactly. I can’t remember it. Even I used this dictionary multiple time.
Who cares about its location?
I believe to give you a direction to find out the location by yourself whenever you forget the location.
Here is the command locate which is used to Find a File in Linux in All Directories. or any specific location.
Use the following command to know the location of rockyou wordlist:
#locate rockyou
See the last line of the result in the above image. the location is /usr/share/wordlists/rockyou.txt.gz
You can confirm the location by using the ls command followed by rockyou wordlist location.
See the Example below
Unzip rockyou.txt.gz into rockyou txt
Have you noticed one thing? The rockyou file has .gz extension of the file. This is not a normal file, this is a zip file. Neither you can see the content from this file nor you can use it.
zip file is not useful anymore. So you need to extract / unzip by using following commands
#cd /usr/share/wordlist/
#ls
#gzip -d rockyou.txt.gz
I hope you have liked this article, If yes then please thumbs up. If you have questions leave in the comment box. Whenever I will get time, reply to you.
Thanks for Reading full article.
Cheers!
If Appreciate My Work, You should consider:
- Join Group for Discussion Facebook Group
- Get your own self-hosted blog with a Free Domain at ($2.96/month)
- Buy a Coffee to Us! Make Small Contribution by Paypal
- Support us by taking our :Online Courses
- Contact me :[email protected]
hcxtools Description
Small set of tools convert packets from captures (h = hash, c = capture, convert and calculate candidates, x = different hashtypes) for the use with latest hashcat or John the Ripper. The tools are 100% compatible to hashcat and John the Ripper and recommended by hashcat. This branch is pretty closely synced to hashcat git branch (that means: latest hcxtools matching on latest hashcat beta) and John the Ripper git branch ('bleeding-jumbo').
Support for hashcat hash-modes: 2500, 2501, 4800, 5500, 12000, 16100, 16800, 16801
Support for John the Ripper hash-modes: WPAPSK-PMK, PBKDF2-HMAC-SHA1, chap, netntlm, tacacs-plus

Homepage: https://github.com/ZerBea/hcxtools
Author: ZerBea
License: MIT
hcxtools Help
hcxtools is a common name of a set of tools, each executes only one specific function, and each has option set.
hcxpcaptool Help
hcxpcaptool shows info of pcap/pcapng file and convert it to other hashformats accepted by hashcat and John the Ripper.
usage:
options:
bitmask for message pair field:
- 0: MP info (https://hashcat.net/wiki/doku.php?id=hccapx)
- 1: MP info (https://hashcat.net/wiki/doku.php?id=hccapx)
- 2: MP info (https://hashcat.net/wiki/doku.php?id=hccapx)
- 3: x (unused)
- 4: ap-less attack (set to 1) - no nonce-error-corrections neccessary
- 5: LE router detected (set to 1) - nonce-error-corrections only for LE neccessary
- 6: BE router detected (set to 1) - nonce-error-corrections only for BE neccessary
- 7: not replaycount checked (set to 1) - replaycount not checked, nonce-error-corrections definitely neccessary
Do not use hcxpcaptool in combination with third party cap/pcap/pcapng cleaning tools!
hcxpsktool Help
hcxpsktool calculates candidates for hashcat based on commandline input, hccapx file and/or 16800 hash file (experimental).
usage:
options:
hcxhashcattool Help
hcxhashcattool calculate PMKs from hashcat -m 2500 potfile.
usage:
options:
wlanhcx2cap Help
wlanhcx2cap converts hccapx to cap.
usage:
options:
wlanhc2hcx Help
wlanhc2hcx converts hccap to hccapx.
usage:
options:
wlanwkp2hcx Help
wlanwkp2hcx converts wpk (ELMCOMSOFT EWSA projectfile) to hccapx.
usage:
options:
wlanhcx2essid Help
wlanhcx2essid merges hccapx containing the same ESSID.
usage:
options:
wlanhcx2ssid Help
wlanhcx2ssid strips BSSID, ESSID, OUI.
usage:
options:
wlanhcxinfo Help
wlanhcxinfo shows detailed info from contents of hccapxfile.
usage.:
options:
wlanhcxmnc Help
wlanhcxmnc help to calculate hashcat's nonce-error-corrections value on byte number xx of an anonce.
usage:
options:
wlanhashhcx Help
wlanhashhcx generate hashlist from hccapx hashfile (md5_64 hash:mac_ap:mac_sta:essid).
usage:
options:
wlanhcxcat Help
wlanhcxcat is a simple password recovery tool for WPA/WPA2/WPA2 SHA256 AES-128-CMAC (hash-modes 2500, 2501).
usage:
options:
input option matrix
wlanpmk2hcx Help
wlanpmk2hcx converts plainmasterkey and ESSID for use with hashcat hash-mode 12000 or john PBKDF2-HMAC-SHA1.
usage:
options:
wlanjohn2hcx Help
wlanjohn2hcx converts john wpapsk hashfiles for use with hashcat hash-modes 2500, 2501.
usage:
options:
wlancow2hcxpmk Help
wlancow2hcxpmk converts pre-computed cowpatty hashfiles for use with hashcat hash-mode 2501.
usage:
options:
wlanhcx2john Help
wlanhcx2john converts hccapx to format expected by John the Ripper.
usage:
options:
wlanhcx2psk Help
wlanhcx2psk calculates candidates for hashcat based on the hccapx file (deprecated: will be replaced by hcxpsktool, soon).
usage:
options:
wlancap2wpasec Help
wlancap2wpasec uploads multiple caps to https://wpa-sec.stanev.org.
usage:
options:
whoismac Help
whoismac shows vendor information and/or download oui reference list.
usage:
options:
hcxtools Usage Example
Show detailed description of hashcat hashfile (NPAAE.hccapx):
Example output:
Show the hash list (format md5_64 hash:mac_ap:mac_sta:essid) of a file (NPAAE.hccapx):

Example output:
Read the file test.pcapng and create the test.16800 file of the PMKID hash for hacking into hashcat with hash mode -m 16800 (-z test.16800):
Example output:
How to install hcxtools
Installation on Kali Linux
Installation on BlackArch
Installation on Debian, Linux Mint, Ubuntu and their derivatives
Screenshots
Tutorials
Related tools
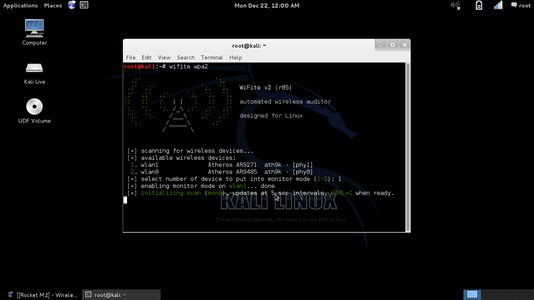
Kali Wifite
- WiFite (51.2%)
- mdk3 (51.2%)
- Aircrack-ng (Suite of Tools) (51.2%)
- Aircrack-ng (Tool) (51.2%)
- infernal-twin (51.2%)
- wifiphisher (RANDOM - 51.2%)